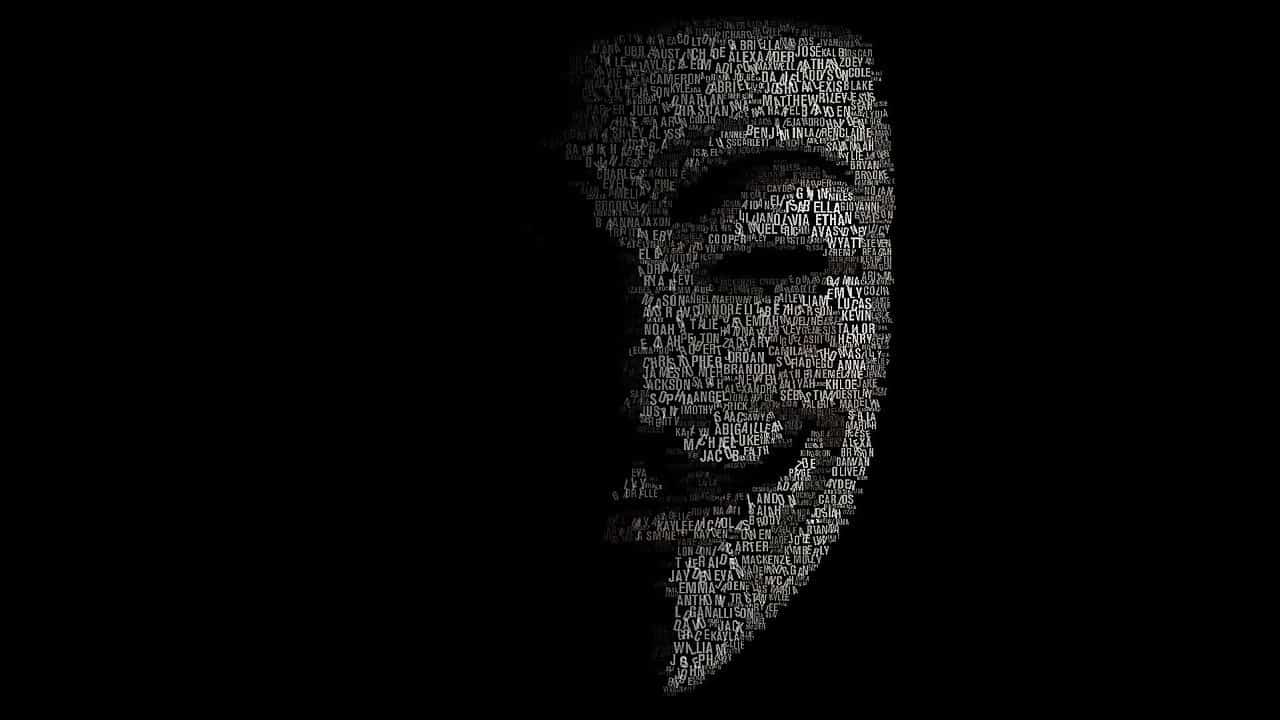
With the rapid evolution of technology and brilliant innovations come an expensive price: Cybercrime. As navigating through our tech-driven world became much easier, vulnerabilities have grown much bigger as well. It is those little backdoors that hackers look to exploit and find their ways into private systems and networks
Cybercrime is not to be taken lightly. Each and every one of us has big chunks of personal information on the network that can be used in the most vindicate ways. Alas, hackers will find a way to use this information against users and for their own benefit. We all know about them, but not all of us are aware that there are different types of them as well.
The thing is, not all hackers are criminals. Some are skilful programmers who use hacking techniques for a good cause, like stopping cybercrimes. Different types of hackers mean using different methods and tactics to do a task. Here is an interesting list of the different types of hackers out there.
1. Black Hat
Needless to say, hackers are people who want to stay anonymous. In movies and shows, those who want to be unseen usually wear black hats. And, that brings us to one of the types of hackers that go first on the list, a black hat hacker. It is pretty much what you may picture when thinking of a disguised criminal but in a different kind of way.
Black hat hackers are cybercriminals with vindictive intentions to cause serious damage. They are the ones behind all the data breach, information theft, and systems destruction. This hacker type is deemed the most dangerous, especially to organizations and large businesses.
2. White Hat
Well, a person in a white hat doesn’t look as intimidating as one in a black hat, right? White hat hackers are just as skilful as black hat ones, but they happen to work on the opposite end of cybercriminals. It is deemed among the good types of hackers.
A white hat hacker is an authorized one hired to encounter malicious attacks and spot vulnerabilities in the cybersecurity system before invaders do. In other words, they are the superheroes of the digital world, threatening to abort the vengeful attacks of cybercriminals and halting their destructive plans.
3. Gray Hat
The types of hackers are plentiful. There’s the white hat hacker and the black hat hacker, and then there’s the grey hat hacker. Pretty much as the name suggests, this type of hacker is neither this nor that. In other words, a grey hat hacker is not a criminal, yet their hacking techniques are neither authorized nor legal as well.
This hacker type is one with great skills that they use for personal enjoyment. Their hacking activities are done just for fun and not for the purpose of causing damage. However, these kinds of hackers, despite being harmless, violate the laws. They are sometimes hired by organizations who are looking to gain publicity by using unlawful methods.
4. Blue Hat
The colour blue identifies the types of hackers that you can hardly put a label on. It is hard to tell whether a blue hat hacker is among the ones with good intentions or malicious ones. This term is usually used to describe revenge seekers. They put their hacking skills into use in order to get back at someone for some personal reason.
On the other hand, the term also describes someone who is hired by an organization to run some bug tests and fix weaknesses in a system before it is aired. This hacker type is also referred to as a security professional. They help organizations and firms strengthen their digital presence and launch well-protected systems and networks.
5. Green Hat
Green hat describes the type of hackers that have just gotten into the aggressive world of hacking. In other words, they are the inexperienced bunch of newbie hackers that this type is sometimes referred to as Hacker-in-Training.
It is really hard to identify this colour as either criminals or authorized ones. They are still eager learners, obtaining brand new information about the malicious side of the web. How they put their skills into use once they manage to elevate into any of the more skilful types of hackers is what determines their intention.
The lack of awareness of a green hat hacker can lead them to cause some disastrous damages. They may launch some vindictive malware during their learning process. The worst part is when they don’t have the needed knowledge to undo the harmful damages they inflicted. It is really being a newbie in the hacking community, especially when this beginner is unaware of what their practice could bring on themselves.
6. Red Hat
Red is the last colour in the spectrum of the types of hackers. It is not the last type though, but the other ones are not identified by colours. So, red hat hackers are, just like the white hat hackers, here to save the digital world. They work on encountering the attacks of cybercriminals and fix the damages inflicted on different systems and networks.
If they do the same thing that white hat hackers do, then why there are two different colours, you may ask. Well, there is a slight yet huge difference between those two types of hackers. They both save the world, but they use different techniques to do so.
The red hat hackers are ones that don’t mind going down an illegal route to make their goals happen. They are commonly referred to as the Robin Hoods of the internet security world. A red hat hacker can use some harmful tactics but always for a good reason.

7. Cryptojacking
Cryptojacking is a combination between the words “cryptocurrencies” and “hijacking.” It is one of the types of hackers specialized in financial theft. With cryptocurrencies, like bitcoins, being the new world’s top investments, they now have cybercrimes solely dedicated to this part.
Cryptojacking hackers are cybercriminals that manage to get into the victim’s system, mining all the available cryptocurrencies they could. They launch their attack by invading the target’s browser and launching pop-up windows. The worst part is that they can keep consuming your resources even if you have closed your browser.
8. Gaming
Gaming is a broad industry that invoked the existence of brand new types of hackers, known as gaming hackers. Some of them are getting into this field to go after users’ sensitive data. Others steal gaming points or extra lives for the game. However, both can be equally dangerous.
Gaming is one of the ways that hackers invade a system, being able to steal personal information. Online gaming requires the gamer to provide several personal data to create a profile. Not to mention that gamers may enter their credit cards to purchase games, increasing the risks of being stolen.
9. Script Kiddies
Script kiddies is a term used by the skilled types of hackers to describe the newbies of the hacking world with little to no experience. However, not all beginners are referred to as script kiddies. A script kiddie is a hacker that uses scripts or programs, developed by other skilful hackers, to launch their attacks.
This hacker type may not possess the same skills of a professional, yet they are still threatening. Script kiddies can still steal sensitive information, breach data, and cause some serious damages. They just do it using more primitive methods and basic tools.
10. Malicious Insider (Whistleblower)
A malicious insider is one of the most dangerous types of hackers, especially in big organizations. It describes someone who is a former employee or business partner to a specific organization who turned out as a traitor. This person may not be a professional hacker but is someone who used to have authorized access to a system and misused it, breaking the ethical code.
Malicious insiders are also known as whistleblowers and can be used to describe double agents. The term can refer to someone who still works within an organization but imposes a real threat on its security. This hacker type is one who leaks sensitive information, leaving the company more prone to financial blackmailing and fraud attacks.
