AI and Data Science: All You Need to Know
Artificial intelligence (AI) and data science are two of the hottest topics in the current tech...
Read onHow to Be a Cybersecurity Engineer? Your Full Guide to Getting Started
You’re ready to take on the world as a newly-minted cybersecurity engineer. You have new...
Read onThe Various Types of Malware and How to Protect Yourself From Them
Hackers use numerous means to conduct a cybersecurity attack; they constantly develop these methods to...
Read onPrivilege Escalation and How to Prevent it
One of the most common security vulnerabilities that are both easy to happen and usually...
Read onSoftware Firewall Vs. Hardware Firewall: Which One Should You Choose?
Which is better, software firewalls or hardware firewalls? Which one do you need? But first,...
Read onIs a CISSP Certificate Worth it? 7 Reasons Why You Should Get it
The total workforce in the cybersecurity field is 4.7 million, yet this growing field still...
Read onFirewall Exceptions: Everything You Need to Know!
How to add firewall exceptions to your device? Here is a better question, should you...
Read onWhat Is a Network Security Key?
What is a network security key? Before answering this question, here is an interesting fact:...
Read onHow to Devise the Best Cybersecurity Plan for Your Business
In the face of increasing cyber threats, organisations can protect themselves by applying proper cybersecurity...
Read onWhat to Do if You Click on a Phishing Link? 5 Life-Saving Steps
Malware includes a wide array of tools that hackers use to steal sensitive information from...
Read onWhat Is a Keylogger and How to Detect It on Android Phones
The increasing use of mobile phones motivated hackers to develop new hacking tools that will...
Read onHow to Prevent a Data Breach? 9 Crucial Steps to Follow
Data breaches have unfortunately been on the rise in the past few years, and the...
Read onHow to Beat Ransomware?
Cybercriminals keep developing their attack methods to keep up with the developments in cybersecurity. Their...
Read onWhat is an Operating System ?
An operating system (commonly abbreviated with the terms OS) is a basic software used to...
Read onMachine Learning vs Artificial Intelligence vs Deep Learning: What is the Difference
It’s difficult to have a single, unified definition for artificial intelligence (AI), machine learning (ML),...
Read onYour Guide to the Different Types of Computer Networks
Networks are the real heroes behind the increased demand for computers and other technological devices...
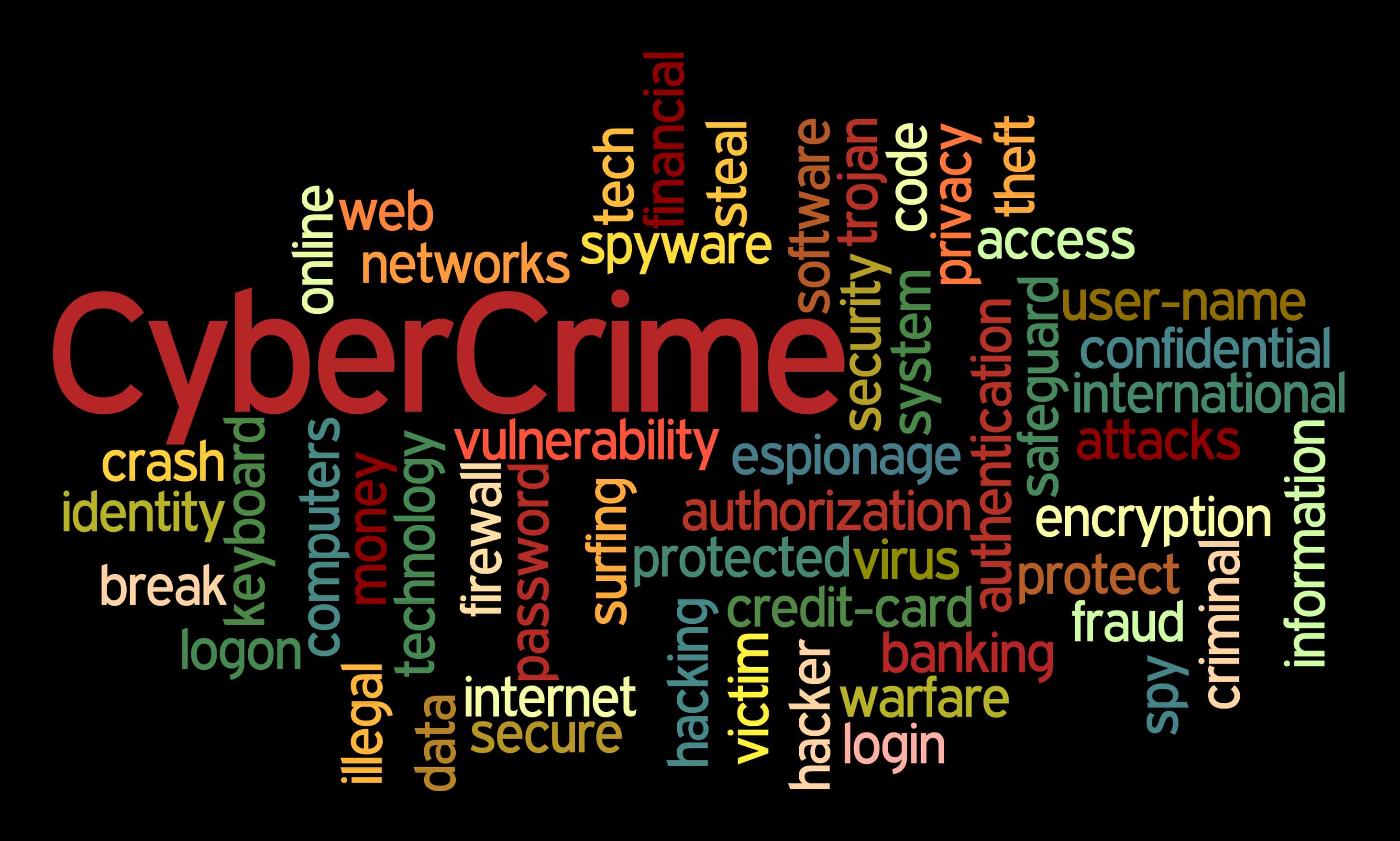
Read onCybercrime Terminology You Should Know
Cybercrime is increasing rapidly nowadays. The terminology used to describe it is evolving accordingly. By...
Read onArtificial Intelligence: Types and Examples
Science has been constantly surprising us with the new advancements it introduces the world to....
Read onCybercrime Investigation: Techniques & Tools
The number of cybercrime is dramatically increasing nowadays. This is due to the increase in...
Read onA Complete Guide to GDPR: 5 Important Facts
Businesses, small or large, have become obliged to protect their online presence. It’s essential for...
Read onData Breach: Definition, 3 Types, Causes, and More
Many businesses managed to thrive and prosper thanks to everything the digital world has offered....
Read on9 Common Malware Types and Best Protection Programs
Being online has become an essential part of our daily lives. Even businesses have established...
Read onWhat Does Cyber Mean?
Related to Information Technology (IT), “cyber” is a word we frequently see nowadays. From cybersecurity...
Read onHow to Update Your Security Settings
If one asked half a dozen people if they knew about the security settings of...
Read onWhat Is Bebo?
Although Facebook has seemed to revolutionize social media, there were other sites that had the...
Read onHow to Take a Screenshot
There will always be a point in time where you feel the need to take...
Read onWhat is the Spyphone Software?
There are several free applications that are used to monitor the activities of smartphones. One...
Read onHow to Track Text Messages
Text messages and instant messaging are two of the most common ways to communicate with...
Read onHow Tech-Savvy Are You? 4 Facts and More
By definition, being tech-savvy means that a person is fairly proficient in using modern high-tech...
Read onEllo: The Next Big Thing?
The vast world of the Internet is expanding every day. Every day, new websites are...
Read onWhat Is Cloud Computing?
You’ve likely seen the word “cloud” mentioned online or in a television advertisement. It’s also...
Read onThe Myth of Private Browsing
The concept of private Internet browsing is being able to tour and view the Internet...
Read onUnderstanding Internet Privacy
Privacy and the internet do not necessarily go hand in hand. You can take steps...
Read onHow To Delete Facebook
Facebook is one of the most popular social media platforms. It has been around longer...
Read onGeoTagging: Getting a Geographic Handle
Geotagging (also written as GeoTagging) is a technology that allows users to link a photograph,...
Read onHow to Use Twitter
How to Use Twitter: Proper Twitter Usage or the Consequences Proper Use of Social Media Social...
Read onFAQs about Privacy Policy
You always see the blue link that leads to the privacy policy at the bottom...
Read onWhat Is the Data Protection Act?
The Data Protection Act has increasingly drawn in a lot of attention from people throughout...
Read onThe Internet Glossary
In this piece, we are going to give a little information about common Cyber crimes...
Read onWhat is the Internet?
For all of the advancements made possible by the Internet today, only a few years...
Read on